CAMS Research Framework
Successful cybersecurity leadership covers four critical areas shown in the pillars of our research program framework.
Explore the research projects associated with each area by clicking on that pillar.
Click here to see full diagram with list of projects
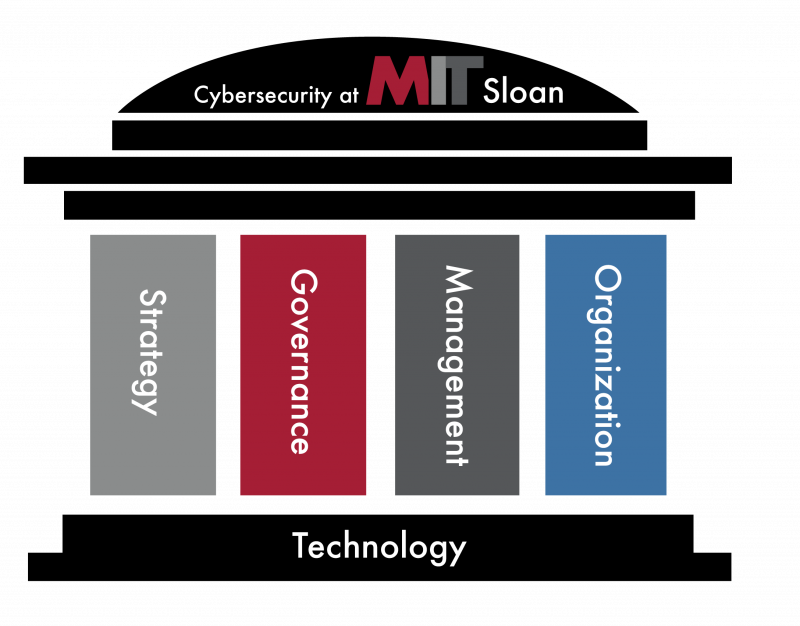
Strategy
- Board’s role in cybersecurity leadership
- Education of Boards and C-levels on cybersecurity
- Structure of cybersecurity workforce
- Prioritizing innovation and cybersecurity together
- Cybersecurity Information and mitigation sharing for competitive advantage
- International trade cybersecurity considerations
Governance
- House of Security: assessing cyber maturity
- Building organizational cybersecurity culture
- Bridging the IT/OT culture gap
- Framework for cyber education
- Ethics of cybersecurity
Management
- Cyber safety: research in accident prevention
- Cybersecurity of Industrial Control Systems (ICS)
- Cloud computing cybersecurity
- Cybersecurity of IoT and autonomous vehicles
- Vulnerability research
- Bridging the IT/OT culture gap
- Smart cities cybersecurity
Organization
- Building organizational cybersecurity culture
- Cyber insurance and risk mitigation
- Comparing national cybersecurity frameworks
- International cyber information sharing processes
- Creating security without sacrificing usability
- Success factors for cybersecurity companies
CAMS Research Framework
Successful cybersecurity leadership covers four critical areas shown in the pillars of our research program framework.
Explore the research projects associated with each area by clicking on that pillar.
Click here to see full diagram with list of projects
CAMS Research Framework
Successful cybersecurity leadership covers four critical areas shown in the pillars of our research program framework.
Explore the research projects associated with each area by clicking on that pillar.
Click here to see full diagram with list of projects
Click here to see full diagram with list of projects
Research Briefs
Visual Research Repository- (IC)3 Research Framework Overview
- Understanding the Cyber Attack Business
- Cybersecurity Culture Maturity Model
- Managing Risk with Cybersecurity Insurance
- House of Security: Assessing Cybersecurity Readiness
- Cybersecurity Concerns in the Adoption of IoT Technology
- Security Threats to Cyber Physical Systems (CPS)
- Cybersecurity and International Trade
- The Business of the Dark Web
- Building a Culture of Cybersecurity
- Cybersecurity Management in Pharmaceutical and Biotechnology Industries
- Cybersecurity Management in Pharmaceutical and Biotechnology Industries — one page
- Cybersecurity of IoT using Blockchain: Endpoint Security
- Understanding the Risks in the Mobility-as-a-Service Industry
- Balanced Scorecard for Cybersecurity Management
- Zero Trust Networks
- The Cyber Risk Cube
- Cybersecurity of AI Systems
- Fire Drills and Tabletop Exercises
- EarFisher: Detecting Wireless Eavesdroppers
- SolarWinds as a Cybersecurity Game Changer
- The Convergence and Divergence of Regulatory Compliance and Cybersecurity
- Designing Cybersecurity into Digital Offerings
- Simulating Attack Scenarios
- Cybersecurity for Small and Medium Businesses
Posters & Presentations
Visual Research Repository
- Human Centered Interface Design for a Dynamic Cyber-Risk Group-Based Training Game, by Tony Delvecchio, Sander Zeijlemaker, Giancarlo De Bernardis and Michael Siegel. Published in Computer Standards & Interfaces, Volume 95, 2026, 104030, ISSN 0920-5489
- Categorizing Differences in Cyber Incident Reporting Definitions and The Impact on Regulatory Compliance by Dr. Angelica Marotta & Dr. Stuart Madnick
- If Companies Are More Prepared, Why Are Breaches Still Rising? by Stuart Madnick, originally published in The Wall Street Journal, presented at CCIS 2024.
- How Leaders Can Create a Cybersecure Workplace Culture by Keri Pearlson and Stuart Madnick, originally published in The Wall Street Journal, presented at CCIS 2024.
- An Action Plan for Cyber Resilience by Michael Coden, Martin Reeves, Keri Pearlson, Stuart Madnick, and Cheryl Berriman, originally published in MIT Sloan Management Review, presented at CCIS 2024.
- A Tool to Help Boards Measure Cyber Resilience by Keri Pearlson, originally published in Harvard Business Review, presented at CCIS 2024.
- 4 Areas of Cyber Risk That Boards Need to Address by Sander Zeijlemaker, Chris Hetner, and Michael Siegel, originally published in Harvard Business Review, presented at CCIS 2024.
- Human-Centered Interface Design for a Cyber-Risk Group-Based Training Game by Tony Delvecchio, Sander Zeijlemaker, Giancarlo De Bernardis and Michael Siegel, presented at CCIS 2024.
- Are Boards the Weak Link? by Jeff Proudfoot and Keri Pearlson, originally published in The Wall Street Journal, presented at CCIS 2024.
- A New FAIR Method to Boost IT/OT Infrastructure Resilience by Ranjan Pal, Sander Zeijlemaker, and Michael Siegel, presented at CCIS 2024.
- (Gen)AI for Cybersecurity via a Lense of Business Strategy by Cynthia Zhang, Ranjan Pal, Corwin Nicholson, and Michael Siegel, presented at CCIS 2024.
- (Gen)AI vs (Gen)AI in Industrial Control Cybersecurity by Cynthia Zhang, Ranjan Pal, and Michael Siegel, presented at CCIS 2024.
- Can Wall Street Solve the Cyber-Security Problem? by Ranjan Pal, Stuart Madnick, and Michael Siegel, presented at CCIS 2024.
- Quantifying and Optimizing ICS Cyber-Resilience (CR) by Ranjan Pal and Michael Siegel, presented at CCIS 2024.
- Cybersecurity Regulation Development and Dissemination Deficiencies Harming Organizational Cybersecurity Outcomes by Jeff Proudfoot and Stuart Madnick, presented at CCIS 2024.
- Optimizing Cyber Investments by Solving the Risk-Reward Paradox by Goeun Kim, Sander Zeijlemaker, Jeff Proudfoot, Ranjan Pal, and Michael Siegel, presented at CCIS 2024.
- Combat Future AI-Powered Cyber Threats Using Digital Twin Simulations by Sander Zeijlemaker, Michael Siegel, Michiru Ishikawa, Abhishta Abhishta, Yasir Hak, and Annet Chau, presented at CCIS 2024.
- The Global Matrix of Cybersecurity Compliance: An Analysis of Regulatory Synergies by Angelica Marotta and Stuart Madnick, presented at CCIS 2024.
- Culture and the Supply Chain: Aligning Cybersecurity Values, Attitudes, and Beliefs across Supply Chains by Jillian Kwong and Keri Pearlson, presented at CCIS 2024.
- Cybersecurity Culture Maturity Model by Mridula Prakash and Keri Pearson, presented at CCIS 2024.
- AI Impact on Cybersecurity Culture by Mridula Prakash and Keri Pearlson in partnership with KPMG, presented at CCIS 2024.
- Exploring Shortcomings in Third Party Risk Management of Small and Medium-Sized Enterprises (SMEs) by Jillian Kwong and Keri Pearlson, presented at the October 2023 Members Only Meeting.
- Misalignment and Mismatch: Cybersecurity Complexities of Small to Medium-Sized Enterprises (SMEs) in the Supply Chain by Jillian Kwong and Keri Pearlson, presented at the October 2023 Members Only Meeting.
- Combatting The Risk Reward Paradox to Manage Cyber Risk by Goeun Kim, Sander Zeijlemaker, and Michael Siegel, presented at the October 2023 Members Only Meeting.
- Decision Making Ransomware Capability Development: Persona-Driven Simulation Approach by Prem Sagar, Sander Zeijlemaker, and Michael Siegel, presented at the October 2023 Members Only Meeting.
- Supplier Development Framework in Supply Chain Cybersecurity Evaluation of Small and Medium-sized Enterprises (SMEs) by Alex Chang, Jillian Kwong, and Keri Pearlson, presented at CCIS 2023.
- Cyber Risk Management Support Tools by Angela Mgbeke, Sander Zeijlemaker, and Michael Siegel, presented at CCIS 2023.
- A Flood of New Regulations Are Coming: Do You Have Your Lifeboats Ready? by Angelica Marotta and Stuart Madnick, presented at CCIS 2023.
- Securing the Global Supply Chain: Addressing Risks Small and Medium-sized Enterprises (SMEs) Pose to Cybersecurity Supply Chains by Jillian Kwong and Keri Pearlson, presented at CCIS 2023.
- Board Level Balanced Scorecard for Cyber Resilience by Mridula Prakash and Keri Pearlson, presented at CCIS 2023.
- Insights on Cybersecurity Governance And Risk Management for Boards of Directors by Jeff Proudfoot and Stuart Madnick, presented at CCIS 2023.
- Boosting Resilience Within IT/OT Network Architecture by Ranjan Pal, Sander Zeijlemaker, and Michael Siegel, presented at CCIS 2023.
- AI in Cybersecurity as a Business Strategy by Cynthia Zhang, Ranjan Pal, Corwin Nicholson, and Michael Siegel, presented at CCIS 2023.
- Cyber Resiliency in Naval Engineering Systems (Updated) by Ryan Montvydas and Keri Pearlson, presented at CCIS 2023.
- Cyber Risk Governance as a Differentiator in Resilience by Sander Zeijlemaker, Michiru Ishikawa, and Michael Siegel, presented at CCIS 2023.
- Perusing Watermelon Risks to Strengthen Cyber Resilience by Sander Zeijlemaker, Ranjan Pal, and Michael Siegel, presented at CCIS 2023.
- Cyber Resiliency in Naval Engineering Systems by Ryan Montvydas and Keri Pearlson, presented at CCIS 2022.
- (Catastrophic) Business Cyber Risk Management by Ranjan Pal, Stuart Madnick, and Michael Siegel, presented at CCIS 2022.
- Case Studies of How Cybersecurity Can Create a Competitive Advantage by Keri Pearlson and Jonathan Muniz, presented at CCIS 2022.
- Investigating Regulatory Operationalization and Its Impacts on Cybersecurity by Jeff Proudfoot and Stuart Madnick, presented at CCIS 2022.
- Next Generation of Cyber Risk Management Dashboards by Sander Zeijlemaker, Michael Siegel, and Angela Mgbeke, presented at CCIS 2022.
- APT-Induced IT/OT Cyber Risk Quantification by Ranjan Pal, Sander Zeijlemaker, and Michael Siegel, presented at CCIS 2022.
- Balanced Scorecard Dashboard for Cybersecurity by Mridula Prakash and Keri Pearlson, presented at CCIS 2022.
- Longitudinal Breach Research by Sander Zeijlemaker, Michiru Ishikawa, and Michael Siegel, presented at CCIS 2022.
- Supply Chain Cybersecurity for Small and Medium Enterprise by Alex Chang and Jillian Kwong, presented at CCIS 2022.
- Are You Adequately Protecting Against Increasing COVID-19 Cyber Threats? by Michael Coden, BCG and CAMS Research Affiliate, presented to the CAMS Friday Research Meeting March 27, 2020.
- Risk Management During COVID-19 by Ron Ford, DHS, presented to the CAMS Friday Research Meeting, March 27, 2020
- PreventOTPhysDamage: Anticipating and Preventing Catastrophic OT Physical Damage Through System Thinking Analysis by Shaharyar Khan and Stuart Madnick, presented at CREDC 2020.
- Evaluating Effectiveness of an Embedded System Endpoint Security Technology on EDS: Defeating the Hackers of IIoT Devices: by Matt Maloney, Michael Siegel, Greg Falco, and Elizabeth Reilly. Presented at CREDC 2020.
- Scenario-Based Simulator for Operational Resilience During a Cyber Attack by Keman Huang and Michael Siegel presented at CREDC 2020.
- A Smart IoT Integrity – First Communication Protocol via an Ethereum Blockchain Light Client presented to the 1st International Workshop on Software Engineering Research & Practices for the Internet of Things (SERP4IoT 2019) by Elizabeth Reilly, Matthew Maloney, Michael Siegel, and Gregory Falco, March 27, 2019.
- Status Update: Research Exploring Malware in Energy Delivery Systems (REMEDYS) presented to CREDC by Michael Sapienza and Keri Pearlson, February 15, 2019.
- GDPR Update – presented to Cybersecurity at MIT Sloan Research Team by Emerald de Leeuw, November 16, 2018.
- Cutting Edge Cybersecurity Leadership Research at MIT’s Sloan School – presented to the Society of Information Management (SIM) Boston Summit, October 23, 2018
- Creating a Cybersecurity Culture: (ISC)2 Survey Responses – presented to The International Information System Security Certification Consortium (ISC)2 October 8, 2018 by Keri Pearlson.
- Blockchain for Defensive Social Engineering – presented to Society of Information Management (SIM) April 12, 2018 by Greg Falco
- Building a Cybersecurity Culture: A Measurement Model and a Maturity Model – presented to Society of Information Management (SIM) Cybersecurity Special Interest Group February 2018 by Keri Pearlson
- Studying the Tension Between Digital Innovation and Cybersecurity – as presented at the AMCIS conference, August 2017, by Natasha Nelson and Stuart Madnick.
- PreventOTPhysDamage: Anticipating and Preventing Catastrophic OT Physical Damage Through System Thinking Analysis – as presented at the CRED-C conference, March 2017, by Matt Angle, Stuart Madnick, James L. Kirtley, and Nabil Sayfayn.
- The Wolves of Vuln Street: The 1st System Dynamics Model of the 0day Market – as presented at the RSA Conference, April 21, 2015, Moscone Center, by Michael Siegel and Katie Moussouris of HackerOne.
- Cyber Safety: A Systems Thinking and Systems Theory Approach to Managing Cybersecurity Applied to TJX Case – as presented at the International Atomic Energy Agency, Vienna, June 2, 2015, by Qi Van Eikema Hommes, Hamid Salim, Stuart Madnick, and Michael Coden.
- Advancing Cybersecurity Using System Dynamics Simulation Modeling For System Resilience, Patching, and Software Development (download) – as presented September 3, 2014, by Michael Siegel and James Houghton.
- Advancing Cybersecurity Using System Dynamics Simulation Modeling For Analyzing & Disrupting Cybercrime Ecosystem & Vulnerability Markets – as presented September 3, 2014, by Michael Siegel and James Houghton.
- Cyber Safety: A Systems Thinking and Systems Theory Approach to Managing Cybersecurity Applied to TJX Case – as presented by Hamid Salim and Stuart Madnick on September 3, 2014, by Stuart Madnick and Hamid Salim.
- MIT House of Security and Measurement of Security Perceptions in Corporations and Organizations – as presented on September 3, 2014 by Stuart Madnick.
Early Research Papers
(Members have access to current white papers and additional recently published papers on the Members Only page) Visual Research Repository
- “Rethinking the Cybersecurity Arms Race : When 80% of Ransomware Attacks are AI-Driven” by Michael Siegel, Sander Zeijlemaker, Vidit Baxi and Sharavanan Raajah. Working Paper. April 2025 This Working Paper is being updated based on some recent reviews. We expect the updated version to appear here shortly.
- ‘The Cyber Risk Cube: A New Tool for Cybersecurity Risk Management” by Michael Siegel and Kristin Chen. Working Paper. November 2021.
- “Trusting the Needle in the Haystack: Cybersecurity Management of AI/ML Systems” by Sanjana Skukla, José Ignacio Parada, and Keri Pearlson. (Copyright Notice: This manuscript is scheduled for publication at the Future of Information and Communication Conference (FICC) 2022.)
- “The Cybersecurity Skills Survey: Response to the 2020 SIM IT Trends Study” by Chris Maurer, Mary Sumner, Dan Mazzola, Tim Jacks, and Keri Pearlson. June 2021.
- “A Systematic Framework to Understand Transnational Governance for Cybersecurity Risks from Digital Trade” by Keman Huang, Stuart Madnick, Nazli Choucri, and Fang Zhang. June 2021.
- “Convergence and Divergence of Regulatory Compliance and Cybersecurity” by Angelica Marotta and Stuart Madnick. June 2021.
- “Applying the Lessons from the Equifax Cybersecurity Incident to Build a Better Defense” by Ilya Kabanov and Stuart Madnick. June 2021.
- “Cybersafety Approach to Cybersecurity Analysis and Mitigation for Mobility-as-a-Service and Internet of Vehicles” by Chee Wei Lee and Stuart Madnick. May 2021.
- “Cybersecurity Management of AI Systems” by Keri Pearlson, Sanjana Shukla, and Ignacio Parada. May 2021. (White Paper)
- “Cyber Range for Industrial Control Systems (CR-ICS) for Simulating Attack Scenarios” by Shaharyar Khan, Alberto Volpatto, Geet Kalra, Jonathan Esteban, Tommaso Pescanoce, Sabino Caporusso, and Michael Siegel. Presented at the ITASEC conference 2021.
- “Building a Security Propaganda Machine: The Cybersecurity Culture of Verizon Media” by Keri Pearlson (CAMS), Sean Sposito, Masha Arbisman, and Josh Schwartz (Verizon Media), February 15, 2021.
- “Preparing for Cyber Breaches with Fire Drills and Table Top Exercises” by Keri Pearlson, Brett Thorson, Stuart Madnick and Michael Coden. Submitted to Harvard Business Review, February 7, 2021.
- Sneak peek: “From Bolted-On to Baked-In: Designing Cybersecurity into Digital Offerings” (Full Paper) by Dr. Keman Huang and Dr. Keri Pearlson, in progress, January 28, 2021.
- Sneak peek: “A Major Breakdown of International Trade and Next Global Financial Crisis: Could be Caused by Efforts to Prevent Cyberattack on the Web” by Stuart Madnick and Keman Huang, In-progress, 2021.
- Sneak peek: “Development of a Research Plan to Understand the Role of Compliance in Improving or Hindering Cybersecurity in Organizations” by Stuart Madnick and Angelica Marotta, In-progress, 2021.
- “Varieties of Public-Private co-governance on cybersecurity within the digital trade: Implications from Huawei’s 5G” by Keman Huang, Matthew Deegan, Stuart Madnick, Fang Zhang, and Michael Siegel. 2021.
- “A Culture of Cybersecurity can be Your Competitive Advantage” by Keri Pearlson and Keman Huang (CAMS), December 20, 2020.
- “Does High Cybersecurity Capability Lead to Openness in Digital Trade? The Mediation Effect of of E-Government Maturity” by Keman Huang and Stuart Madnick, November 2020
- “Building Global Digital Supply Chain Hub by Cybersecurity Commitment: Singapore’s Strategic Role in the Digital Age”, by Keman Huang, Stuart Madnick, and Nazli Choucri. Submitted in Global Policy (Online), October 2020.
- “Cybersecurity Culture at C6 Bank Case Study” by Keri Pearlson, Madeline Li and Sarah Chou, October 14, 2020 (CAMS Teaching Case Study)
- “Cybersecurity Management of AI/ML Systems” by Keri Pearlson, George Wrenn, and Sanjana Shukla, September 2020.
- “The Impact of Corporate Values and Factors of Internal and External Culture on Formulating the Post-COVID “New Normal” : Implications for Cybersecurity and Information Systems” by Leonardo Castro, Keri Pearlson, Daniel Gozman, and Ganna Pogrebna, September 2020 (CAMS White Paper)
- “Cybersecurity Management of AI Systems: Managing an Attempted Breach at E-Fortress Capital” by Keri Pearlson, George Wrenn, and Sanjana Shukla, June 2020 (Case Study).
- “Inter-sector network and clean energy innovation: Evidence from the wind power sector”, by Fang Zhang, Tian Tang, Jun Su, Keman Huang. Published in the Journal of Cleaner Production, May 2020.
- “CEO’s Cybersecurity Role During COVID19” by Keri Pearlson and George Wrenn, March 20, 2020 (CAMS White Paper)
- “Analyzing the Interplay Between Regulatory Compliance and Cybersecurity” by Angelica Marotta and Stuart Madnick. Presented at the 19th annual Security Conference, Las Vegas (virtual) in March 2020.
- “A Case Study of the Capital One Data Breach” by Nelson Novaes Neto, Stuart Madnick, Anchises Moraes, and Natasha Borges. Presented at the 19th annual Security Conference, Las Vegas (virtual) in March 2020.
- “Cyber Securing Cross Border Financial Services: Calling for a Financial Cybersecurity Action Task Force” by Keman Huang and Stuart Madnick. Presented at the 19th annual Security Conference, Las Vegas (virtual) in March 2020.
- “Cybersafety Analysis of Industrial Control Systems: Chiller Systems” by Shaharyar Khan and Stuart Madnick. Presented at the 19th annual Security Conference, Las Vegas (virtual) in March 2020.
- “Companies Should Stop Telling Employees to Keep Changing Passwords” by Stuart Madnick for The Wall Street Journal, March 2020.
- “How to Safeguard Against Cyberattacks on Utilities” by Stuart Madnick, published in the Harvard Business Review January 2020
- “Cybersafety: A System- theoretic Approach to Identify Cyber-vulnerabilities & Mitigation Requirements in Industrial Control Systems” by Shaharyar Khan, Stuart Madnick, Member, and IEEE, January 2020.
- “Cyber-Physical System Security Automation through Blockchain Remediation and Execution (SABRE)” by Matthew Maloney, Gregory Falco, and Michael Siegel, January 2020.
- “Responding to a Large Scale Energy Delivery Sector Cyber Attack Teaching Packet” (Case and Teaching Note) by Keri Pearlson, Michael Sapienza and Sarah Chou, December 31, 2019 (Submitted to CREDC as final deliverable for REMEDYS project).
- “Building a Model of Organizational Cyber Security Culture: 2019 Survey Results” by Dr. Keman Huang and Dr. Keri Pearlson, December 2019.
- “Casting the Dark Web in a New Light” by Keman Huang, Michael Siegel, and Keri Pearlson. Featured in the MIT Sloan Management Review July 2019 edition.
- “Analysis of Cross-Border Data Trade Restrictions using Mixture-based Clustering” by Keman Huang, Samuel Chinnery, Stuart Madnick, and Keri Pearlson. Presented at AMCIS August 2019.
- “Cyber Physical IoT Device Management” by Matthew Maloney, Elizabeth Reilly, Michael Siegel, and Gregory Falco. July 2019.
- “The Internet of Things Promises New Benefits and Risks” by Mohammad S. Jalali, Jessica P. Kaiser, Michael Siegel, and Stuart Madnick. April 2019.
- “A Culture of Cybersecurity at Banca Popolare di Sondrio” by Angelica Marotta and Dr. Keri Pearlson. March 01, 2019.
- “Identification and Mitigation of Cyber Vulnerabilities in Industrial Control Systems using a System Theoretic Design Approach” by Shaharyar Khan. January 2019.
- “Responding to a Large Scale Energy Sector Cyber Attack Case Study” by Keri Pearlson, Michael Sapienza and Sarah Chou, December 31, 2019 (Teaching note available upon request).
- “Research Plan to Analyze the Role of Compliance in Influencing Cybersecurity in Organizations” by Stuart Madnick, Angelica Marotta, Nelson Novaes, and Kevin Powers. December 2019.
- “Framework for Understanding Cybersecurity Impacts on Digital Trade” by Keman Huang, Stuart Madnick, and Simon Johnson. December 2019.
- “Building a Model of Cybersecurity Culture: Survey Results” by Keman Huang and Keri Pearlson, December 20, 2019.
- “Blockchain Isn’t as Unbreakable as You Think” by Stuart Madnick. Published in Sloan Management Review, November 2019.
- “Casting the Dark Web In a New Light” by Keman Huang, Michael Siegel, Keri Pearlson and Stuart Madnick. Published in Sloan Management Review, July 2019.
- “Identifying and Anticipating Cyber Attacks that Could Cause Physical Damage to Industrial Control Systems” by Matthew G. Angle, Stuart Madnick, James L. Kirtley Jr., and Shaharyar Khan. June 2019.
- “Health Care and Cybersecurity: Bibliometric Analysis of the Literature” by Mohammad S. Jalali, Sabina Razak, William Gordon, Eric Perakslis, and Stuart Madnick. February 15, 2019.
- “The Internet of (Wonderful and Scary) Things” by Mohammad Jalali. January 2019.
- “For What Technology Can’t Fix: Building a Model of Organizational Cybersecurity Culture” by Keman Huang and Keri Pearlson. January 2019.
- “Enhancing Cybersecurity Education through High Fidelity Live Exercises (HiFLiX)” by Johan Sigholm, Gregory Falco, and Arun Viswanathan. September 2018.
- “For What Technology Can’t Fix: Building a Model of Organizational Cybersecurity Culture” by Keman Huang and Keri Pearlson. 2018.
- “Cyber negotiation: a cyber risk management approach to defend urban critical infrastructure from cyberattacks” by Gregory Falco, Alicia Norieha, and Lawrence Susskind published in Journal of Cyber Policy. December 17, 2018.
- “Systematically Understanding the Cyber Attack Business: A Survey” by Keman Huang, Michael Siegel, and Stuart Madnick. July 2018.
- “Cyber Insurance as a Risk Mitigation Strategy” by Michael Siegel, Nadya Bartol, Juan Jose Carrascosa Pulido, Stuart Madnick, Michael Coden, Mohammad Jalali, and Michael Bernaski. April 2018. A brief accompanying this report is also available here.
- “A Framework for Systematically Understanding the Cyber Attack Business” by Keman Huang, Michael Siegel, and Stuart Madnick. January 24, 2018.
- “Profiling the Organizational Cybersecurity Culture: Toward a Cybersecurity Culture Framework” by Keman Huang and Keri Pearlson. January 2018.
- “Cyber Resiliency in Hospitals: a Systematic, Organizational Perspective” by Mohammad S. Jalali and Jessica Paige Kaiser. January 2018.
- “Measuring Stakeholders’ Perceptions of Cybersecurity for Renewable Energy Systems” by Stuart Madnick, Mohammad S. Jalali, Michael Siegel, Yang Lee, Diane Strong, Richard Wang, Wee Horng Ang, Vicki Deng, and Dinsha Mistree. In book: Lecture Notes in Artificial Intelligence 10097, 2017, 67–77.
- “Trust and Collaboration to Enhance Cybersecurity” by Keman Huang, Keri Pearlson, and Stuart Madnick. December 14, 2017.
- “Decision Making and Biases in Cybersecurity Capability Development: Evidence from a Simulation Game Experiment” by Mohammad S. Jalali, Michael Siegel, and Stuart Madnick. December 2017.
- “The Internet of Things (IoT) Promises New Benefits — and Risks: A Systematic Analysis of Adoption Dynamics of IoT Products” by Mohammad S. Jalali, Jessica Paige Kaiser, Michael Siegel, and Stuart Madnick. November 2017.
- “Cybercrime-as-a-Service: Identifying Control Points to Disrupt” by Keman Huang, Michael Siegel, and Stuart Madnick. November 2017.
- “Beyond Keywords: Tracking the evolution of conversational clusters in social media” by James P. Houghton, Michael Siegel, Stuart Madnick, Nobuaki Tounaka, Kazutaka Nakamura, Takaaki Sugiyama, Daisuke Nakagawa, and Buyanjargal Shirnen. October 2017.
- “Decision Making and Biases in Cybersecurity Capability Development: Evidence from a Simulation Game Experiment” by Mohammad S. Jalali, Michael Siegel, and Stuart Madnick. August 2017.
- “The Internet of Things (IoT) Promises New Benefits — And Risks: A Systematic Analysis of Adoption Dynamics of IoT Products” by Mohammad S. Jalali, Jessica Paige Kaiser, Michael Siegel, and Stuart Madnick. August 2017.
- “Identifying and Mitigating Cyber Attacks that could cause Physical Damage to Industrial Control Systems” by Matthew G. Angle, Stuart Madnick, and James L. Kirtley, Jr. August 2017.
- “Cybersecurity Information Sharing Incentives and Barriers” by Priscilla Koepke. June 2017.
- “Striking a balance between usability and cyber-security in IoT devices” by Saurabh Dutta. May 2017.
- “Cyber Warfare Conflict Analysis and Case Studies” by Mohan B. Gazula. May 2017.
- “Cybersafety Analysis of the Maroochy Shire Sewage Spill” by Nabil Sayfayn and Stuart Madnick. May 2017.
- “Preparing for the Cyberattack That Will Knock Out U.S. Power Grids” by Stuart Madnick. May 2017.
- “Institutions for Cyber Security: International Responses and Data Sharing Initiatives” by Nazli Choucri, Stuart Madnick, and Priscilla Koepke. April 2017.
- “Studying the Tension Between Digital Innovation and Cybersecurity” by Natasha Nelson and Stuart Madnick. April 2017.
- “Trade-offs between digital innovation and cyber-security” (31 pages) by Natasha Nelson and Stuart Madnick. March 2017.
- “Diversity or Concentration? Hackers’ Strategy for Working Across Multiple Bug Bounty Programs” by Keman Huang, Michael Siegel, Stuart Madnick, Xiaohong Li, and Zhiyong Feng. December 2016.
- “Ukraine Power Grid Cyberattack and US Susceptibility: Cybersecurity Implications of Smart Grid Advancements in the US” by Abir Shehod. December 2016.
- “Analysis of the Digital Direct-to-Customer channel in Insurance” by Nithila Jeyakumar. December 2016.
- “Institutions for Cyber Security: International Responses and Data Sharing Initiatives” by Nazli Choucri, Stuart Madnick, and Priscilla Koepke. August 2016.
- “Cyber Safety: A Systems Theory Approach to Managing Cyber Security Risks – Applied to TJX Cyber Attack” by Hamid Salim and Stuart Madnick. August 2016.
- “Measuring Stakeholders’ Perceptions of Cybersecurity for Renewable Energy Systems” by Stuart Madnick, Mohammad S. Jalali, Michael Siegel, Yang Lee, Diane Strong, Richard Wang, Wee Horng Ang, Vicki Deng, and Dinsha Mistree. August 2016.
- “A Systems Theoretic Approach to the Security Threats in Cyber Physical Systems: Applied to Stuxnet” by Arash Nourian and Stuart Madnick. September 2014.
- “Cyber Safety: A Systems Thinking and Systems Theory Approach to Managing Cyber Security Risks” (Condensed 37 page version) by Hamid Salim and Stuart Madnick. September 2014.
- “Cyber Safety: A Systems Thinking and Systems Theory Approach to Managing Cyber Security Risks” (Full 157 page version) by Hamid Salim. May 2014.
- “Institutional Foundations for Cyber Security: Current Responses and New Challenges” (JITD) by Nazli Choucri, Stuart Madnick, and Jeremy Ferwerda. October 2013.
- “Inter-Organizational Information Sharing of Customer Data in Retail” by John Tengberg. May 2013.
- “Issues in Strategic Management of Large-Scale Software Product Line Development” by Jean-Baptiste Henri Nivoit. May 2013.
- “Challenges in Implementing Enterprise Resource Planning (ERP) system in Large Organizations: Similarities and Differences Between Corporate and University Environment” by Goeun Seo. May 2013.
- “Using System Dynamics to Analyze the Effect of Funding Fluctuation on Software Development” (ASEM) by Travis Trammell, Stuart Madnick, and Allen Moulton. March 2013.
- “Agile Project Dynamics: A System Dynamics Investigation of Agile Software Development Methods” (SD Conference) by Firas Glaiel, Allen Moulton, and Stuart Madnick. March 2013.
- “Towards better understanding Cybersecurity: or are “Cyberspace” and “Cyber Space” the same?” (WISP) by Stuart Madnick, Nazli Choucri, Steven Camiña, and Wei Lee Woon. November 2012.
- “Strategic Philanthropy for Cyber Security: An extended cost-benefit analysis framework to study cybersecurity” by Yiseul Cho. June 2012.
- “Comparative Analysis of Cybersecurity Metrics to Develop New Hypotheses” (WISP) by Stuart Madnick, Nazli Choucri, Xitong Li, and Jeremy Ferwerda. November 2011.
- “Institutional Foundations for Cyber Security: Current Responses and New Challenges” (revised) by Jeremy Ferwerda, Nazli Choucri, and Stuart Madnick. September 2011.
- “Exploring Terms and Taxonomies Relating to the Cyber International Relations Research Field: or are “Cyberspace” and “Cyber Space” the same?” by Steven Camiña, Stuart Madnick, Nazli Choucri, and Wei Lee Woon. August 2011.
- “Experiences and Challenges with using CERT Data to Analyze International Cyber Security” (AIS/WISP) by Stuart Madnick, Xitong Li, and Nazli Choucri. September 2009.
- “Explorations in Cyber International Relations (ECIR) – Data Dashboard Report #1: CERT Data Sources and Prototype Dashboard System” Stuart Madnick, Nazli Choucri, Steven Camiña, Erik Fogg, Xitong Li, and Fan Wei. August 2009.
- “Institutional Foundations for Cyber Security: Current Responses and New Challenges” by Jeremy Ferwerda, Nazli Choucri, and Stuart Madnick. September 2010.
- “A Systems Approach to Risk Management” (ASEM) by Nathan A. Minami, Stuart Madnick, and Donna Rhodes. November 2008.
- “An Economic Analysis of Policies for the Protection and Reuse of Non-Copyrightable Database Contents” (JMIS) by Hongwei Zhu, Stuart Madnick, and Michael Siegel. February 2008.
- “Preventing Accidents and Building a Culture of Safety: Insights from a Simulation Model” by John Lyneis and Stuart Madnick. February 2008.
- “Enhancing Vehicle Safety Management in Training Deployments: An Application of System Dynamics” by Kelvin F. H. Lim. February 2008.
- “The House of Security: Stakeholder Perceptions of Security Assessment and Importance” (FSTC) by Wee Horng Ang, Vicki Deng, Yang Lee, Stuart Madnick, Dinsha Mistree, Michael Siegel, Diane Strong, and Richard Wang. July 2007.
- “Using System Dynamics to Model and Better Understand State Stability” (SD) by Nazli Choucri, Daniel Goldsmith, Stuart E. Madnick, Dinsha Mistree, J. Bradley Morrison, and Michael D. Siegel. July 2007.
- “House of Security: Locale, Roles and Resources for Ensuring Information Security” (AMCIS) by Wee Horng Ang, Yang W. Lee, Stuart E. Madnick, Dinsha Mistress, Michael Siegel, Diane M. Strong, Richard Y. Wang, and Chrisy Yao. August 2006.
- “Improving National and Homeland Security through Context Knowledge Representation & Reasoning Technologies” (Book chapter) by Nazli Choucri, Stuart E. Madnick, and Michael D. Siegel. April 2006.
- “Understanding & Modeling State Stability: Exploiting System Dynamics” (IEEE Aerospace) by Nazli Choucri, Christi Electris, Daniel Goldsmith, Dinsha Mistree, Stuart E. Madnick, J. Bradley Morrison, Michael D. Siegel, and Margaret Sweitzer-Hamilton. January 2006.
- “Understanding & Modeling State Stability: Exploiting System Dynamics” (PCAS Final Report with Appendices) by Nazli Choucri, Christi Electris, Daniel Goldsmith, Dinsha Mistree, Stuart E. Madnick, J. Bradley Morrison, Michael D. Siegel, and Margaret Sweitzer-Hamilton. December 2005.
- “Policy for the Protection and Reuse of Non-Copyrightable Database Contents” by Hongwei Zhu, Stuart Madnick, and Michael Siegel. November 2005.
- “To Standardize Enterprise Data or Not? An Economic Analysis of Flexibility versus Control” by Chander K. Velu, Stuart E. Madnick, and Marshall W. Van Alstyne. November 2005.
- “Context Mediation Demonstration of Counter-Terrorism Intelligence (CTI) Integration” by Stuart E. Madnick, Allen Moulton, and Michael D. Siegel. May 2005.
- “Research Initiative to Understand & Model State Stability: Exploiting System Dynamics” (SD) by Nazli Choucri, Stuart E. Madnick, and Michael D. Siegel. February 2005.
- “Linkage Between Pre- and Post- Conflict: Exploiting Information Integration & System Dynamics” (IEEE Aerospace) by Nazli Choucri, Stuart E. Madnick, Allen Moulton, Michael D. Siegel, and Hongwei Zhu. January 2005.
- “Improving National and Homeland Security through a proposed Laboratory for Information Globalization and Harmonization Technologies” (LIGHT) by Nazli Choucri, Stuart Madnick, Michael Siegel, and Richard Wang. February 2004.
- “Global e-Readiness – For What? Readiness for e-Banking” (Journal of IT Development) by V. Maugis, N. Choucri, S. Madnick, M. Siegel, S. Gillett, F. Haghseta, H. Zhu, and M. Best. April 2004.
- “Improving UccNet-Compliant B2B Supply-Chain Applications Using a Context Interchange Framework” (BAI2004) by Steven Yi-Cheng Tu, Stuart Madnick, and Luis Chin-Jung Wu. February 2004.
- “Information Integration for Counter Terrorism Activities: The Requirement for Context Mediation” (IEEE Aerospace) by Nazli Choucri, Stuart E. Madnick, Allen Moulton, Michael D. Siegel, and Hongwei Zhu. November 2003.
- “LIGHTS: Laboratory for Information Globalization and Harmonization Technologies and Studies” by Nazli Choucri, Stuart Madnick, Michael Siegel, and Richard Wang. February 2003.
- “Attribution Principles for Data Integration: Technology and Policy Perspectives – Part 2: Focus on Policy” by Thomas Lee. February 2002.
- “Attribution Principles for Data Integration: Technology and Policy Perspectives – Part 1: Focus on Technology” by Thomas Lee. February 2002.
- “Why Not One Big Database? Principles for Data Ownership” (DSS) by Marshall Van Alstyne, Erik Brynjolfsson, and Stuart Madnick.
Why Join Cybersecurity at MIT Sloan?
Benefit from usable research! Cybersecurity at MIT Sloan (CAMS), formerly (IC)3, is focusing MIT’s uniquely qualified interdisciplinary faculty and researchers on the fundamental principles of cyberspace, cybercrime, & cybersecurity applied to critical infrastructure. Cybersecurity at MIT Sloan is a confidential academic forum in which leaders and managers can benefit from the experiences of CSO/CISOs across multiple sectors.
Community

Cybersecurity at MIT Sloan
Contact Us
Professor Stuart Madnick, Director, smadnick@mit.edu
Dr. Michael Siegel, Director, msiegel@mit.edu
Administration : dagmar@mit.edu
Communications : kcfitz@mit.edu
© Copyright 2025
Cybersecurity at MIT Sloan (CAMS) Privacy Statement
MIT Captioning & Accessibility